Computer hackers take to the cloud
Online data storage services often — and unknowingly — host malicious software

The term cloud computing suggests data stored in the upper atmosphere. In fact, they are really housed in enormous banks of computers known as a server farm.
buchachon / iStockphot
In recent years, computing has gone to the cloud. But this so-called “cloud computing” can pose new risks, a study finds. The reason: Computers that make up the cloud have become a hideout for malware, programs that can hijack or harm someone’s computer or files.
People use “cloud computing” to free up space on their own computers. They can store files containing anything from research data to vacation snapshots. Some people also run programs on devices connected through the cloud, rather than on their own, personal machines. This cloud computing, therefore, makes it possible for someone to share files quickly with a lot of other people.
But for all its benefits, the cloud can have a dark side. That’s a finding of the new study. Malware stored on devices that make up the cloud can turn on — and against you — when you click on certain fraudulent website links or when you download an attachment that masks its real intent. These links or attachments will trick the user, linking its computer to files in some cloud where malware lurks.
“If you’re on a website and you click on a button, is that a good button or a bad button?” asks Christopher Fletcher. He is a computer scientist at NVIDIA (En-VID-ee-ah), a technology company in California. The bad news, he warns: “Malware is everywhere.”
Raheem Beyah was part of the new investigation into cloud-based malware. This computer engineer works at the Georgia Institute of Technology in Atlanta. He and his co-workers searched for malware in files stored by 20 different companies that store people’s data. Those include cloud services owned and operated by Google (like Google Drive) and Amazon.
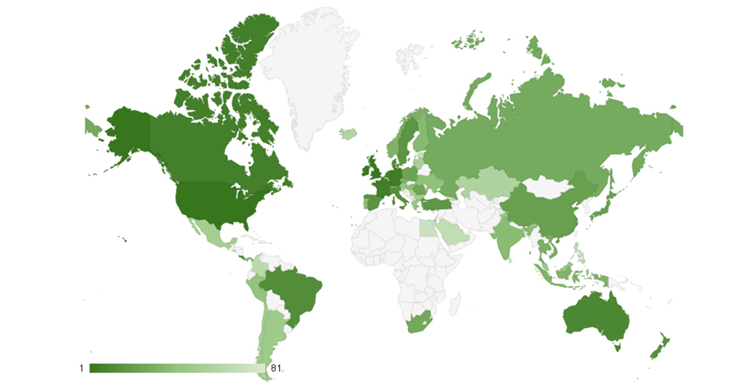
In all, the researchers probed about 150,000 websites. These sites linked to cloud repositories. A repository is like a personal locker that stores someone’s files. Every cloud hosting service had some repositories that contained malware, the new study found. The researchers scanned 6,885 repositories and confirmed that 694 contained malware. That means malware lurked in about one out of every 10 repositories that had been scanned. They called these dangerous sites “bars.” That’s short for “bad repositories.”
Story continues below map.
The malware that hackers store in bars is the same type that can infect personal computers, Beyah says. Hackers have simply moved beyond individual machines to infiltrating cloud services, he concludes. Members of his team presented findings from their study on October 24 at a computer security conference in Vienna, Austria.
Masked malware
Users can’t tell the difference between good programs and malware, Fletcher says. That’s why he likes the new study by Beyah’s group. It identified malware and now offers guidance for how to find it – and avoid it in the future. Moreover, he points out, that new study “sheds some light on what malware looks like.”
And that’s important because bars are often disguised. The malware they hold may be fragmented, with pieces stored in different repositories. So scanning any one repository with security software may fail to identify a problem. What’s more, many bars contain small computer programs that act like bodyguards. These programs prevent security-scanning software from even seeing what is inside.
But Beyah and his co-workers used that knowledge to their advantage. To find bars, they built a scanner to scout for those software bodyguards. Normal repositories don’t have them.
The bodyguards may have hidden bars from other researchers, “but it gave them away to us,” Beyah says. Without those bodyguard programs, the scientists might have missed the bars. For people who store data online or use cloud computing, Beyah offers some tips. Scan cloud files from time to time using malware-detection software. And try to think like a hacker, especially if you have computer skills. “Pretend to be a hacker and figure out if there’s a way to break into your own site,” he says. “That’s a good exercise.”
For now, Beyah is skeptical of cloud computing security. As soon as a new technology emerges, attackers find a way in, he says. That’s why he won’t store files online unless he’s not worried about who sees them or has encrypted them before loading them onto the cloud. (Encryption is a way to hide the contents of the file and keep them safe from hackers.)