How computers get out the vote
For elections to succeed, communities must be able to count every vote — and do it accurately
Voting technology matters in every election.
Fredex8/iStockphoto
Every two years, on the first Tuesday after a Monday in November, people across the United States gather at their local polling sites to vote. Each time, they’ll choose a representative for Congress. Depending on their state and what year it is, some might also be asked to vote for a senator and state and local officials. Many voters may even get to choose yes or no on a specific issue (such as whether to approve taxes for schools and parks).
Most importantly, every four years people entering those voting booths will be asked to select someone for the highest office in the land: president.
The outcome of all of these elections depend on how people vote. At one level, that refers to the choices people make on their ballots. But it also can have a lot to do with the process — how those people vote. And this is where technology matters.
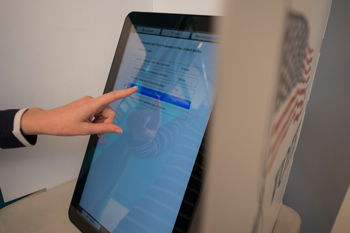
Computers play some role in virtually all major U.S. elections. Sometimes they star. In some polling booths, for instance, people may touch a computer screen, selecting each candidate and answer to a displayed question.
Other times, those machines may lurk in some back room, outside of the polling place. Their job may be simply to “read” paper ballots.

But how safe and reliable are those computers? By now, everyone knows these machines can be hacked. And do computerized systems fully protect voters’ rights?
In late 2000, the United States waited for weeks to learn whether former Texas governor George W. Bush or outgoing vice president Al Gore would be president. The decision seemed to pivot on whether computers might have misread some ballots in Florida. Under the system used then, voters punched holes in prescored paper ballots. But many ballots had hanging bits of paper left by incomplete hole punches. Did a partial punch signal someone’s true choice? (These bits of paper came to be known as “hanging chads.”)
Some states have now gone back to having people vote by coloring in ovals on a paper ballot. But even here a computer usually steps in to scan the ballots and tally the votes.
All of these methods, and the hassles they involve, seem somewhat low-tech in our internet age. Yet most states don’t let people vote online in a general election unless the voter is overseas or in the military (where mailed responses may not reliably arrive back in time). Most places don’t even let people vote on a computer anymore unless the system also produces a paper backup for each vote.
Cumbersome as these systems are, there are good reasons to be careful. A good voting system must do a lot more than simply tally votes. People have to trust that cheaters can’t rig the process. There should be ways to double-check the results. And the system must protect a voter’s privacy.
New systems to achieve this are in the works. They, too, rely on computers. And they are using the technology in new ways to not only provide accuracy, but also privacy and new types of ballot security.
Online voting?
People make choices on the internet every day. And scientists who have surveyed the general public find most people could easily use such a system.
In one study, researchers at Rice University in Houston, Texas, had people vote in a mock election. Those who used their smartphones made fewer errors than did those who used another computer system. Still, the team did not recommend a widespread switch to vote-by-phone systems.
Claudia Ziegler Acemyan is a psychologist at Rice. “Mobile voting is not ready for federal, state and local elections due to security concerns,” she says.
And here’s why. “Yes, you can order a pizza online. Yes, you can play games online. You can do your banking online,” says Caitriona Fitzgerald. She is the chief technology officer and state policy coordinator for EPIC. That’s the Electronic Privacy Information Center, based in Washington, D.C. Those online systems she mentioned “are not necessarily 100 percent secure. And with our elections,” she argues, “we need to make sure it’s 100 percent secure.”

Data breaches have become almost common. They have taken place at Facebook, credit card companies, online stores and many other businesses. Government agencies have had their files read and copied by spies and thieves. The Democratic National Committee was even hacked in 2016 and many of its emails leaked online.
Voter information is not always safe either. In August 2016, the Federal Bureau of Investigation reported that hackers had gotten into online voter registration files for the state of Illinois. Later reports suggested people had illegally tried to break into voter databases held by more than 20 states.
Messing with voter-registration files could cause hassles and delays for people at the polls. Some might be prevented from voting at all. But blocking or tampering with people’s actual votes could be as bad — or worse. The government might have no way to make things right if people’s votes are stolen or altered. Depending on the circumstances, the outcome of an election might be called into question. The true winner might never be known.
Privacy is another big worry. In the United States, Fitzgerald notes, “We have the right to a secret ballot.” But the technology now available for online voting does not provide the security needed to protect a voter’s right to a secret ballot, she points out.
How secure is online voting?
In the United States, it is illegal for someone to “buy your vote” — that is, pay someone to vote a certain way. And laws exist to keep someone from being threatened — coerced (Ko-URSED) — into voting one way or another. The concept of a secret ballot is designed to prevent such coercion, says David Dill. He’s a computer scientist at Stanford University in Stanford, Calif.
He also founded the Verified Voting Foundation in Carlsbad, Calif. In August, his group, along with EPIC and Common Cause in Washington, D.C., released a new report. Privacy is linked to the integrity, or honesty, of elections, the groups point out. But states cannot yet guarantee the privacy of online voting, their report finds.
“We want people to be able to vote freely,” Dill says. “We don’t want them to be paid for their votes, and we don’t want them to be threatened if they vote differently from whoever is threatening them.” For now, some states ask the limited number of people allowed to vote online to agree to give up that right. Other voters, though, may not know that states cannot yet guarantee the privacy of their online votes.

The good news: Researchers are getting closer to being able to provide such a guarantee. In September 2016, the British company Smartmatic announced that it had been working with a company in the East European nation of Estonia to create a secure and anonymous way for people to vote online.
“Our system allows voters to verify electronically that their vote was cast as intended,” says Ernesto Parisca. He’s a company spokesperson based in Miami, Fla. “This verification is done from a different device from that in which the vote was cast.”
One method is a bit like the two-step process used by Twitter and some other websites. With those systems, when a user signs in, a special number is sent to their phone. To access their account, the user has to enter that number into the website. A version of this new system was tried out as an option to let people cast online votes earlier this year in Utah. These people were voting to select whom state Republicans would back at the July 2016 party convention in Cleveland, Ohio.
Voting by mail actually presents more concerns than online voting, Parisca argues. Each person who opens mail gets to see the votes. Those people would be election officials, though — not hackers. However, those votes still could be stolen while moving through the mail, or fraudulent ballots could be posted in a voter’s name.
It’s not yet clear how experts elsewhere will rate the Smartmatic system. But even if an online system is well-designed, that won’t prevent problems if a hacker got into someone’s computer or phone, Dill and Fitzgerald say. A virus or other malware might copy and transmit how someone voted or did other things online, for example. Then the vote would no longer be private. Malware might even let a hacker change votes or otherwise mess with someone’s ability to cast a vote.
Even a selfie from a voting booth makes some experts worry. In September 2016, a federal court ruled that New Hampshire couldn’t prevent the phone photos. In its view, the ban wrongly limited the right to free speech. But others said a photo might be used as proof for someone who engaged in vote-buying or coercion. The U.S. Supreme Court might eventually rule differently in that or another case.
Leaving a paper trail
“We humans are prone to error,” notes Rui Santos. He’s a computer scientist at Smartmatic’s office in Panama City, Panama. Using computers helps avoid vote-counting errors. Worries arise, however, when there is no paper trail (ballots that can be reviewed one-by-one after a disputed election).
As of September 2016, parts of 15 U.S. states were using all-electronic voting machines with no paper printouts. “Why should we trust votes that are counted on these electronic machines?” Dill asks. “I could think of a thousand ways to make a machine like that cheat,” he says. And yes, he adds, those cheats “would be very difficult to detect.”
For older machines, the crime could take place quickly. Andrew Appel is a computer scientist at Princeton University in New Jersey. An online video shows how he broke into a computer-based voting machine. This Sequoia AVC Advantage device has been used in New Jersey and some other states. In just a few minutes, Appel installed software that altered how the machine worked. This software could change vote tallies — without the voter or officials realizing anything was wrong.

Polling officials control access to voting machines, Santos notes. Those people have a duty to guard against break-ins. All Smartmatic machines used in the United States meet strict standards and provide paper records of votes, this company spokesman says.
But clever hackers may beat the safeguards. Machines can malfunction. Software can have glitches. That’s why many election officials now argue that backup paper records are essential. “Those copies mean that if something goes wrong, we have a lot of opportunity to fix it,” says Dan Wallach. He’s a computer scientist at Rice University.
Here’s what happens: Computers add up and report the votes cast on them, either directly or using some optical scanner. For each election, officials also go through a sample of the paper ballots. A fuller audit and recount can be done if the results from this partial audit don’t match, or if the margin of victory in a race is small. A complete recount could even take place if there were a serious doubt that the vote count had been accurate.
Crafting better computers
Few scientists would argue that computers don’t provide real benefits for voting. They count and add faster — and more accurately — than people do. Computers also can be easier to use by people with some disabilities, such as those who may be blind, deaf or missing a limb. And with paper backups, machine reports and paper ballots act as checks on each other.
Computers also can make voting more convenient. Today, most people have to show up within approved hours at a government-selected polling site. It may be far from where they work. Or there could be long lines. Or it may not be open when a voter will be home. But Wallach, Acemyan and other researchers are working to create a computer system that would let voters cast a ballot from anywhere in a county. They call their pilot voting system STAR-Vote.
The researchers are working to develop it with the help of officials in Travis County, Texas (where the city of Austin is located). This system wouldn’t need voters to go to the one spot named as their polling place. They could vote from any polling place in the county. People who work in downtown Austin, for instance, might choose to vote there, rather than near their homes in the suburbs.
But any polling machine must still be tamper-proof. Toward that end, STAR-Vote and other newer voting computers use advanced encryption. That’s the math of secret codes. “Think about a ballot as just a bunch of 1’s and 0’s,” says Wallach. A 1 is a vote for someone. A 0 means a voter didn’t choose that person. When someone casts a vote, the computer encrypts it so no one peeking into the system would know which person or resolution someone had voted for. Encryption protects the privacy of each vote.
“We want anybody to look at every ballot and be able to add them up without knowing how anybody voted but still get the right answer,” Wallach explains. To do that his group uses a trick called homomorphic encryption. It lets people do math with encrypted numbers without decoding them first.
The process works a bit like the way you can multiply numbers written as logarithms, Wallach explains. A logarithm is the power, or exponent, to which a base number must be multiplied by itself to produce another number. You can add the logarithms of two numbers to multiply them, even if you don’t have a table handy to figure out the base number.
Ideally, voting computers also should use cryptography in clever ways to make it easier for people to confirm that no one tried to rig the system. For example, various equations in the STAR-Vote program wouldn’t work out right if someone tried to hack into the system. “You would actually be able to notice that the system was attacked and realize that something iffy is going on here,” explains Acemyan at Rice.
User friendly
No matter what the voting technology, people should be able to use it easily, Acemyan says. “Ballots where you fill in bubbles on a piece of paper and cast it in a ballot box can be incredibly easy to use if they’re designed right,” Acemyan says. “But so can a voting machine.”
Her research suggests that voting computers can help prevent errors. For example, a program can prevent someone from voting twice. Or, it can remind people if they forgot to vote for a candidate for each office.
Computers also might help boost people’s trust in elections. An end-to-end verifiable system is one that lets people check on its security at every step in the process. That way, election officials would know if someone tried to hack into the system. STAR-Vote would even give people a code that links to their ballot. Voters could then check online to make sure their ballot was recorded, Acemyan says. Because of privacy concerns, however, this system would not show the actual vote.

Research will continue into how voting systems might be made better. One of Acemyan’s recent studies looked at how polling places are set up. Among other things, people said they would be more likely to vote if dividers separated voters from each other. In contrast, people did not like a set-up where they would vote with their backs to the door. That position would let people behind them peek at what they were doing.
Ultimately, researchers hope their work will help boost voter turnout. Only about 57 percent of eligible people voted in the 2012 U.S. presidential election. Only 41.9 percent of voters cast ballots in the 2014 congressional elections. The more people who vote, the more the outcome will represent a community as a whole.
But technology is only one part of the answer to improving election outcomes. Having informed voters also matters. “It’s important to analyze the facts to know which things are good and which things aren’t, and to make informed decisions,” says Santos. Even those who are too young to vote can have an effect, he adds. Teens and tweens can make their opinions known. And they should encourage every adult they know to vote.
“Some cities and counties have opportunities for teenagers to help out at polling places on election days,” notes Dill. “It’s a great way to find out how elections really work from the inside.” It also allows young people to meet others in their community, he says — and make the election go more smoothly.
In any case, adolescents should be sure to register and vote when they’re old enough. After all, in a democracy, everyone’s vote matters.